No one questions the growth of keys and certificates. The issue is that it’s relatively difficult to measure just how much growth. We know that HTTPS, DevOps, and IoT dramatically increase consumption of keys and certificates. Yet, this rapid growth may not be visible to IT and security teams because of the limitations of many approaches to key and certificate management. To better understand just how much this growth these trends are creating, we decided to ask IT professionals how quickly keys and certificates were growing in their enterprises.
We sponsored a study conducted by Dimensional Research that evaluated current and projected growth rates of keys and certificates for 2016 and 2017. Study respondents included 505 IT professionals that manage these critical cryptographic assets in the U.S., U.K., France and Germany.
Given the overall expansion in encryption throughout the enterprise, the results were not surprising. 86% of these IT professionals saw strong growth in the use of keys and certificates in 2016. Kevin Bocek, VP of security strategy, put this in perspective: “This research shows the dramatic growth in encrypted HTTPS to create secure and authenticated connections for web applications, cloud services and IoT continues to explode.”
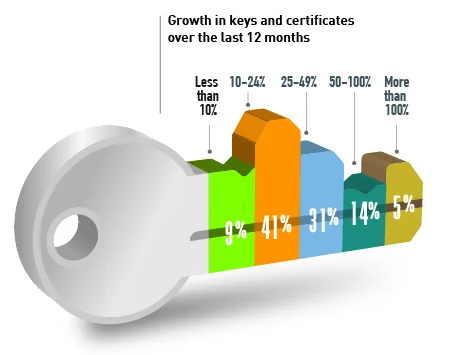
The amount of growth over the previous 12 months is dramatic. In 2016, 50% of respondents saw their key and certificate use grow by more than 25%. And one in five say key and certificate usage increased by more than 50%.
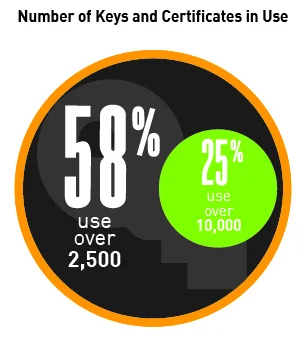
Given this rapid growth rate, organizations could quickly become overwhelmed by the sheer numbers of keys and certificates they must manage and protect. Especially given that 58% say their organizations used more than 2500 keys and certificates in 2016, one in four organizations used more than 10,000 keys. And 88% expect that number to increase up to and above 100% in 2017.
But even these hefty numbers might be a little shy of the actual target. Because of the limitations of certificate authority and manual management methods, organizations are often surprised to learn exactly how many keys and certificates they are actually using. Bocek notes, “Wide spread adoption of DevOps, containers, and cloud services is probably not factored into these growth rates and that means the total number of keys and certificates organizations believe they will use is probably still too low.”
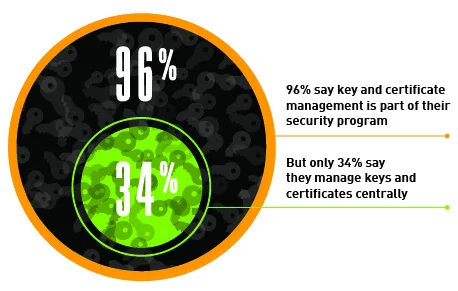
Perhaps the most sobering finding is how many organizations may not be prepared to handle this predicted growth. In the study, 96% reported that key and certificate management is part of their security program. But only 34% say they manage their keys and certificates centrally. Bocek spells out the challenges, “Despite this dramatic growth, more than half of organizations rely on chaotic, error prone, manual processes to protect these critical encryption assets.”
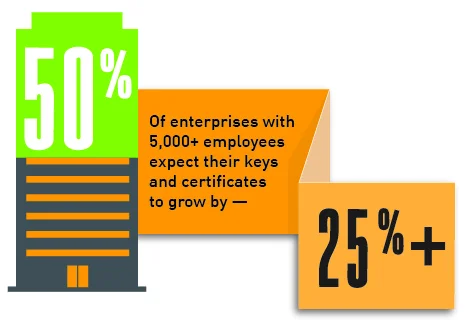
Without proactive attention, the management problems will only get worse. Quickly The study found that 49% predict that key and certificate use will grow by more than 25% over the next 12 months. This is even more apparent in organizations over 5,000, where one in three predicted growth of over 50%. “These dramatic growth rates, combined with organizations’ haphazard approach to protecting keys and certificates presents a golden opportunity for cyber criminals,” warns Bocek.
Cyber criminals remain a threat because most companies are unable to inspect encrypted traffic for attacks. This is due to the inability to intelligently automate and protect the secure distribution of keys and certificates. This gap in security lets cyber criminals easily hide in encrypted tunnels and mask their activities.
Are your keys and certificates safeguarded against an attack that hides in encryption?
Find out why you need machine identity management

2024 Machine Identity Management Summit
Help us forge a new era in cybersecurity
TICKETS ON SALE | Let's get fired up! 🔥 Grab your ticket today and save up to $200 with limited-time Early Bird deals.

