According to McKinsey and company the pandemic has accelerated digital transformation by an average of seven years, and these changes show no signs of slowing. But as our critical infrastructure changes to support the way we need to do business today, our security needs also need to change. Analysts are pointing out key areas of our security programs that need to change keep up with these trends.
In a recent post on Smarter with Gartner, Peter Firstbrook, VP Analyst, Gartner, refers to the immediate impact that digital transformation has on all organizations. “In the past year, the typical enterprise has been turned inside out,” he says. “As the new normal takes shape, all organizations will need an always-connected defensive posture, and clarity on what business risks remote users elevate to remain secure.”
Where previous security strategies focused on protecting the organization at the perimeter, now we need to take security down to the transactional level. We need to focus on protecting every connection and every communication that is in any way associated with our businesses. And the way that we do this is with machine identities that validate every transaction. And all of those machine identities can add up pretty fast.
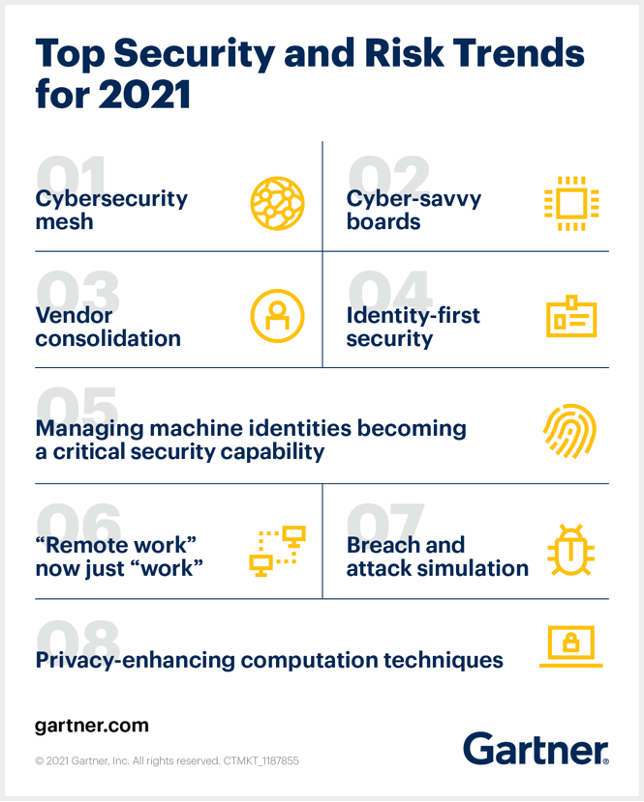
This is one key reason why machine identity management has become a critical component of IAM strategies for organizations everywhere. And now the list of Gartner Top Security and Risk Trends for 2021 highlights these requirements, calling out this top trend as “Managing machine identities as a critical security capability”
The article clarifies, “As digital transformation progresses, organizations are seeing increased numbers of nonhuman entities, which means managing machine identities has become a vital part of the security strategy. Included in machine identities (as opposed to human identities) are workloads (i.e., containers, applications, services) and devices (mobile devices, desktop computers, IoT/OT devices).
As the number of devices increases — and continues to grow — establishing an enterprise-wide strategy for managing machine identities, certificates and secrets will enable the organization to better secure digital transformation.”
As we transform our businesses to become more digital, we are creating unprecedented numbers of connections. And every one of these connections requires a machine identity—whether they are with systems, applications, APIs or cloud native. The end result is a complicated mesh of machine identities that can be difficult to untangle, let alone control. As a result of this rapid growth, machine identity management is increasingly complex—and can directly impact the security posture of all organizations.
A press release from the Gartner Security & Risk Management Summit APAC, notes: “Machine identity management aims to establish and manage trust in the identity of a machine interacting with other entities, such as devices, applications, cloud services or gateways. Increased numbers of nonhuman entities are now present in organizations, which means managing machine identities has become a vital part of the security strategy.”
Here's an engaging way of looking at machine identity management in the context of other top security trends:

The bottom line is that Infosec professionals need to establish and maintain trusted machine-to-machine connections at previously unheard-of scale, across millions and millions of automated interactions. And they must do it at lightning speed. Enterprise-wide machine identity management is only way that organizations can control the chaos machine identity growth.
Are you ready to take on the challenge of managing all of your organizations machine identities? As the global leader in machine identity management, Venafi can help.
Why Do You Need a Control Plane for Machine Identities?
Related posts

2024 Machine Identity Management Summit
Help us forge a new era in cybersecurity
TICKETS ON SALE | Let's get fired up! 🔥 Grab your ticket today and save up to $200 with limited-time Early Bird deals.

![Gartner: Machine Identity Management is a Top Security Trend for 2021 [First Ever] - cover graphic](/_next/image/?url=https%3A%2F%2Fcdn.venafi.com%2F994513b8-133f-0003-9fb3-9cbe4b61ffeb%2F58ca213d-084c-4811-bdff-4d358e938d5a%2Faid_field_img__d0a242d8d9f29b30cf8c7fd66568eb95.jpg%3Fw%3D960%26h%3D540%26fm%3Dwebp%26q%3D85%26fit%3Dcrop&w=3840&q=75&dpl=dpl_CCHxY4sjzWPuuwz2oe2scS3ctPCM)