Earlier this month, the Australia government announced plans to introduce legislation that would force social media and messaging companies to decrypt secure messages. Meanwhile, Germany has broadened their law enforcement's ability to use malware to circumvent encryption as part of active criminal investigations.
Both of these measures were developed to strengthen national security and fight international terrorism. However, experts agree that breaking encryption would do little to prevent terrorist attacks.
Additionally, cyber criminals would certainly take advantage of backdoors imposed on encryption technology. Adversaries are already abusing encryption because most businesses don’t have the tools they need to protect themselves. In 2017, over half of all network attacks will be hidden in encrypted traffic -- this is projected to risk to more than 70% by 2020. As we have seen before, backdoors can, and will, fall into the hands of cyber criminals.
“Giving governments access to encryption will not make us safer from terrorism – in fact, the opposite is true,” says Jeff Hudson, CEO of Venafi. “Most people don’t trust the government to protect data and they don’t believe the government is effective at fighting cybercrime. It’s ironic that we believe we would be safer if governments were given more power to access private encrypted data because this will undermine the security of our entire digital economy.”
The security of encryption is a confusing and technical topic that many IT experts don’t completely understand. So what does the public think about the increasingly contentious debate on encryption technology? Do they believe encryption backdoors will make them safer?
Venafi conducted a study on consumer attitudes and opinions on government backdoors to access encrypted data. One thousand consumers from the United States, United Kingdom and Germany (3,000 total) participated and the results showed that the public is conflicted about the how these laws and policies would affect them personally.
Highlights from the study include:
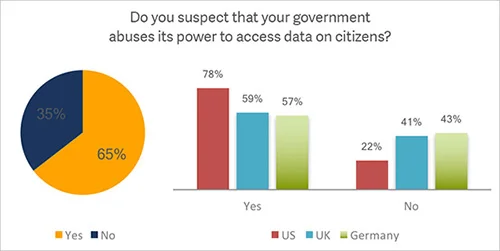
- Are governments abusing powers?
Nearly two-thirds (65%) suspect their government abuses its powers to access the data of citizens.- Respondents from the United States display the most concern; with 78% agreeing abuse may be taking place.
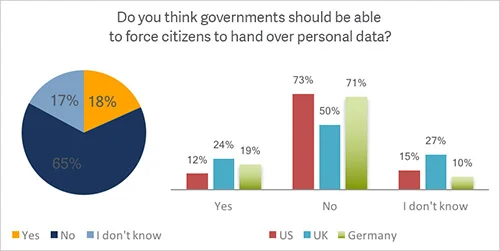
- Should governments require consumer consent?
65% said governments should not be able to force citizens to hand over their personal data, such as the contents of mobile phones, social media, email and online activity, without consent.- However, nearly a quarter (24%) of UK consumers believe their government should be able to access private citizen data without consent.
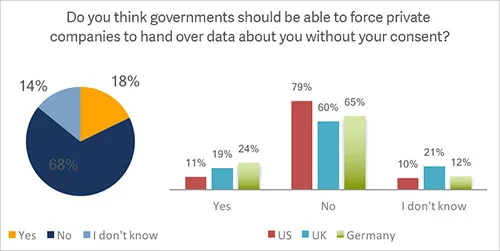
- Should governments force access to encrypted data?
68% said the government should not force private companies to hand over encrypted personal data without consumer consent.
Despite concerns regarding governments’ ability to protect sensitive data and the suspicion that governments already abuse their power to access data on private citizens, consumers remained confused over how encryption backdoors would impact their privacy and national security:
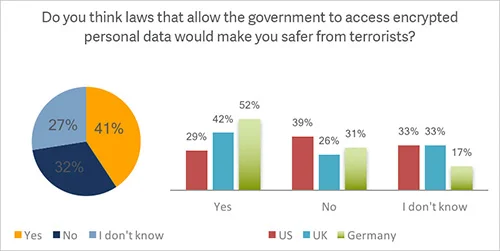
- Will government access to encryption make us safer?
Nearly half (41%) believe laws that provide government access into encrypted personal data would make them safer from terrorists.- Less than a third (29%) of US consumers responded “yes” to this question, however, 52% of German participants agree with this assumption.
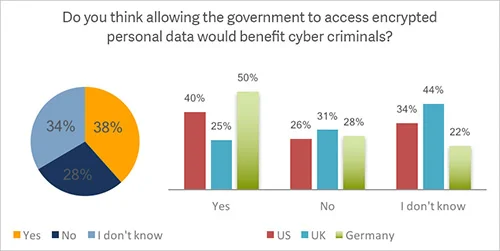
- Will cyber criminals benefit from government access?
Only 38% believe that cyber criminals would benefit if the government had access to encrypted personal data.- Only a quarter (25%) of respondents from the United Kingdom believe cyber criminals would benefit.
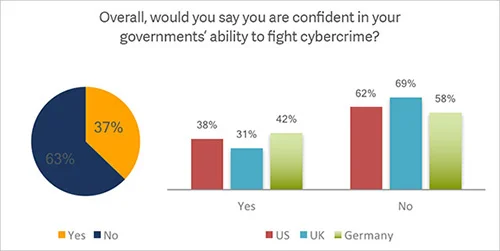
- Can governments successfully fight cyber crime?
Over a third, (37%) are confident in their government’s ability to fight cyber crime responsible for the theft of millions of records of sensitive data.
“The results of this research indicate that security and privacy are probably going to get a lot worse before they get better,” concluded Jeff Hudson. “It’s very clear that consumers are confused about what access to encrypted data will mean to their privacy, and it’s equally clear that governments don’t understand how encryption backdoors will be used to undermine our global digital economy. The negative impact encryption backdoors will have on every aspect of security and privacy is tremendous.”
It’s clear from these results that consumers don’t understand the impact that encryption backdoors will have on their privacy and they are confused about how backdoors can be abused by cybercriminals.
Our increasing reliance on encrypted communication between networks of machines makes identification and authentication between machines critical. Secure and reliable authentication is the only way we can limit encrypted machine-to-machine communication to authorized machines.
What is the technology community’s responsibility in this debate? How can we educate consumers about the threats encryption backdoors bring to their privacy and security?
Find out why you need machine identity management

2024 Machine Identity Management Summit
Help us forge a new era in cybersecurity
TICKETS ON SALE | Let's get fired up! 🔥 Grab your ticket today and save up to $200 with limited-time Early Bird deals.

