Computer encryption is based on the science of cryptography, which has been used as long as humans have wanted to keep information secret. Cryptography is used in securing and protecting data at the time of communication. Before the digital age, the biggest users of cryptography were governments, particularly for military purposes. Cryptography has a long history, dating back to when the ancient Greeks and Romans sent secret messages by substituting letters only decipherable with a secret key.
To carry sensitive information, a system needs to be able to assure secrecy and privacy. A communications system cannot prevent unauthorized access to transmission media absolutely. Data tampering, the act of deliberately modifying the data through an unauthorized channel, is not a new issue, nor it is unique to the computer era. Altering the information could possibly protect it from unauthorized access, and as a result, only the authorized receiver can understand it. Encryption and decryption are the two essential functionalities of cryptography.

TLS Machine Identity Management for Dummies
What is Encryption?
Encryption is the process in which a sender converts the original information to another form and transmits the resulting unintelligible message over the network. The sender requires an encryption algorithm and a key to transform the plaintext (original message) into a ciphertext (encrypted message). Encryption is also known as enciphering.
Plaintext is the data that needs to be protected during transmission. The ciphertext is the scrambled text produced as an outcome of the encryption algorithm for which a specific key is used. The ciphertext is not shielded and it flows on the transmission channel. The encryption algorithm is a cryptographic algorithm that inputs plain text and an encryption key and produces a ciphertext.

What is Decryption?
Decryption inverts the encryption process in order to convert the message back to its original form. The receiver uses a decryption algorithm and a key to transform the ciphertext back to the original plaintext. Decryption is also known as deciphering.
A decryption algorithm is a mathematical process utilized for decryption that generates original plaintext as an outcome of any given ciphertext and decryption key. This is the reverse process of the encryption algorithm.
Encryption and Decryption Keys
Keys are random strings of bits created specifically for ciphering and deciphering data. The keys used for encryption and decryption could be similar and dissimilar depending on the type of cryptosystems used (Symmetric key encryption and Asymmetric or Public-key encryption). Each key is unique and created via an algorithm to make sure it is unpredictable. Keys are usually generated with random number generators or computer algorithms that mimic random number generators.
Symmetric Key refers to those algorithms that make use of the same secret keys for the purpose of both encryptions of plain text and decryption of the ciphertext.
Asymmetric Key refers to those algorithms that make use of two pairs of the key for the purpose of encryption. The public key is made available to any random person, whereas the secret, a private key is made available only to the receiver of the message.
Public Key refers to an asymmetric encryption system that requires two pairs of keys to work. The public keys are the keys that are used to encrypt the message(s) for a recipient.
Private Key refers to the second part of an asymmetric key pair. The private key is the key given to the recipient so only they can decrypt the message.
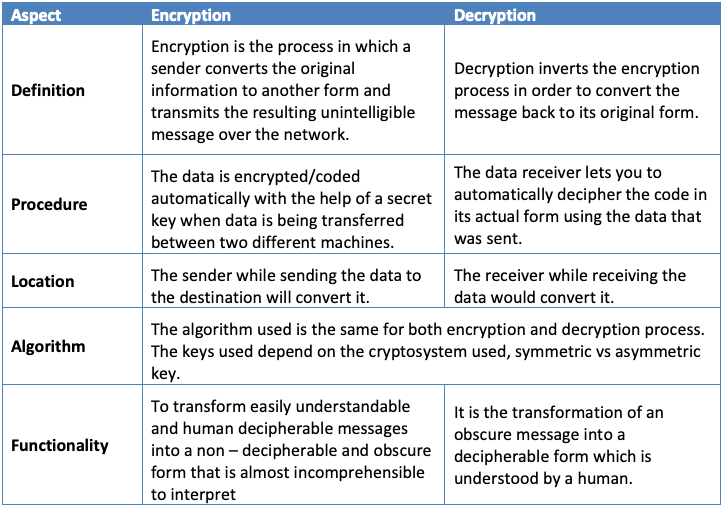
Key differences between Encryption and Decryption
Below are the key differences between encryption and decryption:
- The encryption algorithm uses an original message in a human-readable form, called plaintext, and a key during the encryption process, which transforms the plaintext into an unintelligible and obscure form that cannot be interpreted. Whereas during the decryption process, the decryption algorithm transforms the encrypted form of the message, the ciphertext, using the secret key into a comprehensible form that could be easily understood by a human.
- Encryption occurs at the end of the sender, which is called the source, and decryption occurs at the end of the receiver, which is called the destination.
- The main functionality of encryption is the conversion of plaintext into ciphertext, whereas decryption’s main functionality is the conversion of the ciphertext into plaintext.
- Encryption takes place automatically at the source when data is being sent by a machine. Programs that are pre-installed transform the original information into an encrypted form prior to sending.
- Decryption takes place at the machine of the destination. The machine receives and transforms the encrypted form of the data into the original form.
- Both are both interrelated to each other and they are considered as the cornerstones of preserving the confidentiality, integrity and availability of the data.
The above differences can be summarized in the following table.
Conclusion
Cryptography is critical in preserving data integrity in cyberspace. Encryption and decryption is the most common practice to protect delicate information from hackers or other threats. Encryption is the practice of converting plain text using an algorithm to prevent outsiders from accessing the information. Decryption is the practice of reversing the encrypted text to make it readable to the recipient. All of this is done with keys, public and private.
Get a 30 Day Free Trial of TLS Protect Cloud, Automated Certificate Management.
Related posts
- The Evolution of 256-Bit Encryption and Security Certificates
- What Is Symmetric Encryption?
- Homomorphic Encryption: What Is It and How Is It Used

2024 Machine Identity Management Summit
Help us forge a new era in cybersecurity
TICKETS ON SALE | Let's get fired up! 🔥 Grab your ticket today and save up to $200 with limited-time Early Bird deals.

