When you interact with the Internet of Things (IoT) – like putting on a smart watch or using smart home appliances – you may be inviting hackers into your life.
Lots of IoT devices = lots of threats
By 2028, it is expected that the worldwide consumer IoT market will grow to $154 billion. These network-connected objects, also referred to as Smart Devices, are frequently linked to a smartphone or tablet through Wi-Fi, Thread, or Bluetooth to automate and improve activities like temperature control, lighting, security, and entertainment in a smart home.
The potential for cyber threats grows along with the use of connected devices, particularly as a wave of new products comes to market with vulnerabilities that could expose users to hacking or data leakage. A home with lots of smart devices could be exposed to more than 12,000 hacking or unknown scanning attacks from across the world in a single week, a new report from Which? has found.
Smaller, more affordable IoT gadgets with a variety of user interfaces typically lack the security measures found on more established computing devices like laptops and smartphones.
Matter was developed with security and privacy as its primary design concepts to overcome this shortcoming. Created by the Connectivity Standards Alliance (CSA), it is a standard for low-cost, low-power wireless network technology for IoT devices. CSA is the same group behind the industry’s existing Zigbee standard.
Why Do You Need a Control Plane for Machine Identities?
What is Matter?
For the consumer, Matter aims to make it easier for IoT devices to connect to one another independent of device vendor or controller type. And, as an IP-based, open-source IoT security standard, it also aims to boost the cyber safety of these connected devices.
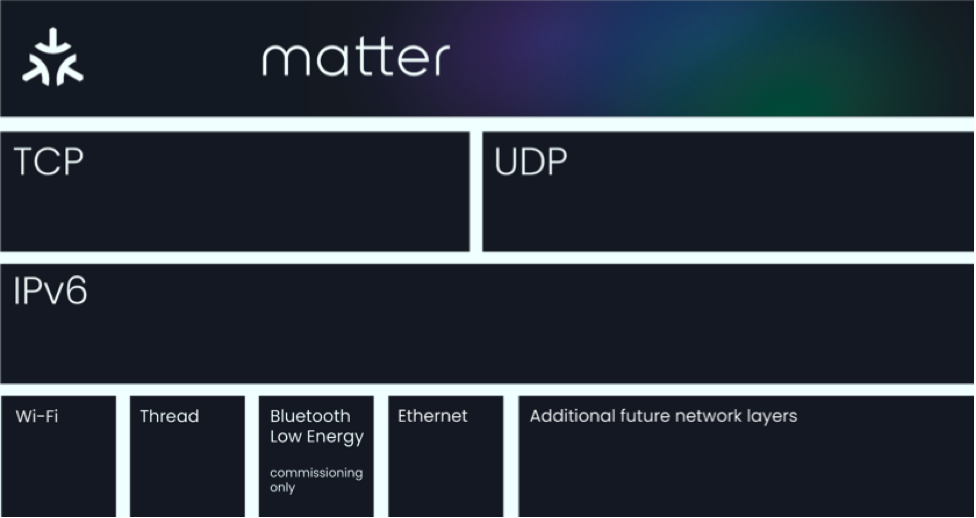
Figure 1: Matter is an application layer protocol. Source: Connectivity Standards Alliance
Matter security
Matter functional security is characterized by the following five characteristics:
- Comprehensive: Implementing layered security with authentication and attestation for commissioning, message encryption, and secure over-the-air firmware updates is required to provide full security.
- Strong: Matter employs a wide range of cutting-edge security measures; standardizes a single, robust cryptography suite based on well-established standards; enables secure sessions for onboarding, attestation, and operation. The protocol additionally utilizes passcodes and digital certificates.
- Easy to use: Matter security is aimed at making it easy for device manufacturers to implement. Consumers that purchase Matter devices will not need to consider security because it is implicit.
- Resilient: The standard specification incorporates several protections against the most frequent denial of service attacks.
- Agile: With crypto-flexibility in mind, Matter can adapt to new threats and advancements. Matter core specification abstracts all cryptographic primitives to allow future editions of the standard to embrace new cryptographic primitives without requiring a complete rewrite of the definition. The modular nature of the protocols also allows for upgrades to new protocols (i.e., quantum safe encryption).
Consumer privacy and encryption
Data privacy is embedded in Matter and the protocol complies with all core privacy principles enacted with the General Data Protection Regulation (GDPR) and subsequent privacy regulations in other parts of the world.
And all Matter devices are required to offer proof of identity by attestation keypair and x.509 certification issued by a Trusted CA so that only recognized Matter entities can communicate data. Encryption ensures that messages and the identity of communicating parties are not sent over the network in plaintext.
Get a 30 Day Free Trial of TLS Protect Cloud, Automated Certificate Management.
Related posts

2024 Machine Identity Management Summit
Help us forge a new era in cybersecurity
TICKETS ON SALE | Let's get fired up! 🔥 Grab your ticket today and save up to $200 with limited-time Early Bird deals.

