Billions of dollars’ worth of transactions are performed across the internet every day. This level of ecommerce can only be made possible if there is a way that we can trust connections across the internet to be secure. Transport Layer Security (TLS) is a widely adopted security protocol that is fundamental to this trust. In fact, TLS puts the security “S” in HTTPS. Due largely to the value of the trust that it enables for internet connections, TLS has become a prime target for cyber criminals, who are eager to abuse the high levels of trust to disguise their own nefarious actions.
But before we explore why cybercriminals place a high value on TLS, let’s talk a bit about what it is and how it works. TLS is designed for securing connections between web clients and web servers over an insecure network. It allows confidential information, such as social security and credit card numbers, or login credentials to be transmitted securely. Without TLS, data sent between clients and servers is sent in plain text, which makes it really easy to be intercepted. Anyone able to hijack the data stream would have unlimited access to the plain text. With properly implemented TLS in place, data is encrypted. So, even if it is intercepted, it cannot be deciphered. That protection is exactly what cybercriminals wish to evade and why they are so eager to get their hands on TLS certificates.

SSL/TLS Certificates and Their Prevalence on the Dark Web
For all of these reasons and more, organizations have relied on TLS to provide the connection security that has enabled today’s unprecedented levels of commerce across the internet. TLS depends on digital certificates to deliver that protection. In other words, TLS certificates serve as machine identities that enable clients to authenticate servers via cryptographic means.
As such, TLS certificates play a critical role in secure and encrypted communications between a client and a server. Organizations must deploy TLS certificates and corresponding private keys to their systems to provide them with unique identities that can be reliably authenticated. The TLS certificate enables anybody connecting to a system to know that they are sending their data to the right place. In addition, it also enables the establishment of secure connections so that no one in the middle can eavesdrop on communications. Given the critical protections that TLS certificates provide, it’s important that organizations protect these valuable security assets so that they don’t fall into the wrong hands.
Grasping the full scale of the certificates you need to manage and protect
How widespread is your use of TLS and how well are you managing it? Many organizations are surprised to discover how many TLS certificates they have. A large enterprise may have tens or even hundreds of thousands of certificates, each identifying a specific server or device in their environment. This is because organizations use TLS not only to secure external connections between themselves and their customers over the internet but also to establish trust between different machines inside their own organization and thereby secure internal communications. Each of these certificates is a potential target for cybercriminals.
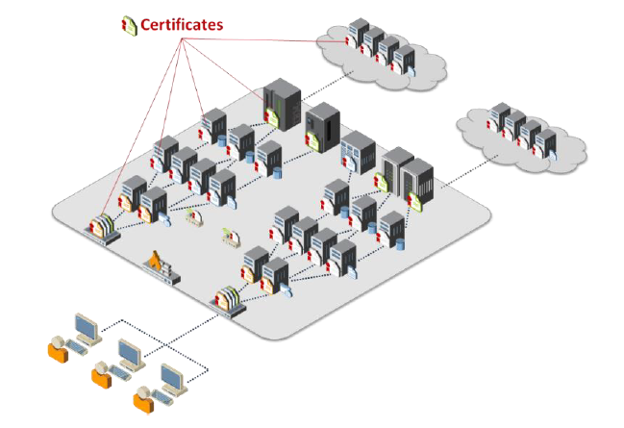
Our growing reliance on machines is one of the factors that have contributed to an explosion in the number of certificates that every organization uses to establish trust. Yet, even though TLS certificates are critical to the security of both internet-facing and private web services, many organizations do not have the ability to centrally monitor and manage their certificates. Instead, certificate management tends to be spread across each of the different groups responsible for the various servers and systems in an organization.
Central security teams struggle to make sure that certificates are being properly managed by each of these disparate groups. This lack of visibility, intelligence and central certificate management service creates a much larger attack surface, that malicious actors are keen to exploit and, hence, puts the organization at greater risk. Organizations that improperly manage their certificates risk system outages and security breaches, which can result in revenue loss, harm to reputation, and exposure of confidential data to attackers.
Why you need to know more about your machine identities than hackers
Machine identities are attractive to attackers because they establish trust. In essence, they verify that a person or an organization is legitimate, and that the TLS certificate belongs to them. This makes end users believe that the session protected by the machine identity is a trusted environment where they can exchange sensitive information such as personal data and financial transactions.
But this protection may also be misused to encourage a false sense of security. As Kevin Bocek, VP of Security Strategy at Venafi, said: “Cyber criminals can now steal money by taking advantage of the one security measure every internet user has been trained to trust: the green padlock in web browsers.”
Despite the pivotal role encryption plays in our digital economy and across the internet, the processes needed to protect digital certificates are not well understood or widely followed. As a result, TLS certificates are often poorly protected, making them easy targets for attackers. In fact, illegitimate access to TLS certificates has played a key role in several high-profile, high-impact breaches—such as Snowden, Sony and Equifax.
Poorly protected and managed TLS certificates can “leak” in the dark web. In fact, recent research sponsored by Venafi highlighted the volume of TLS certificates for sale on the dark web, including information on how they are packaged and sold to attackers. These certificates can be used to eavesdrop on sensitive communications, spoof websites, trick consumers and steal data. The research findings indicate that there is a machine identity-as-a-service marketplace on the dark web, where fraudulent TLS certificates are readily available for purchase.
“This study found clear evidence of the rampant sale of TLS certificates on the dark net,” said Kevin Bocek, vice president of security and threat intelligence for Venafi. “TLS certificates that act as trusted machine identities are clearly a key part of cybercriminal toolkits – just like bots, ransomware and spyware. There is a lot more research to do in this area, but every organization should be concerned that the certificates used to establish and maintain trust and privacy on the internet are being weaponized and sold as commodities to cybercriminals.”
Be sure to stay tuned, as we’ll continue to explore the many ways that TLS certificates can be misused to bypass security and undermine trust within organizations like yours. Plus, you can enjoy complete visibility of your TLS machine identities today with Venafi TLS Protect!
Are you ready to automate your machine identity lifecycles, quickly respond to vulnerabilities, and much more? Contact us.
Get a 30 Day Free Trial of TLS Protect Cloud, Automated Certificate Management.
Related posts
- Attacks Using Machine Identities are Rising Dramatically: Is Your Organization Prepared?
- Microsoft Fixes 2-Year-Old Spoofing Vulnerability after Malware Authors Exploit It in the Wild
- Lemon_Duck and FritzFrog: The Latest Cryptominers Using SSH to Target Servers in the Cloud

2024 Machine Identity Management Summit
Help us forge a new era in cybersecurity
TICKETS ON SALE | Let's get fired up! 🔥 Grab your ticket today and save up to $200 with limited-time Early Bird deals.

